搜索结果: 31-45 共查到“国际动态 计算机系统结构”相关记录174条 . 查询时间(2.297 秒)
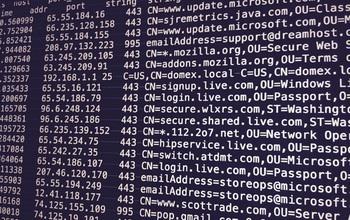
Network Traffic Provides Early Indication of Malware Infection
Network Traffic Early Indication Malware Infection
2017/7/20
By analyzing network traffic going to suspicious domains, security administrators could detect malware infections weeks or even months before they're able to capture a sample of the invading malware, ...

Under Cyber Attack:UH Researchers Look at How to Catch a ‘Phisher’(图)
Under Cyber Attack UH Researchers Phisher
2017/7/20
As cybersecurity experts scramble to stop another wave of ransomware and malware scams that have infected computers around the world, computer science experts at the University of Houston are “phishin...
Toward “valleytronic” devices for data storage or computer logic systems
valleytronic data storage computer logic systems
2017/3/30
Faster, more efficient data storage and computer logic systems could be on the horizon thanks to a new way of tuning electronic energy levels in two-dimensional films of crystal, discovered by researc...
Whether a nation should retaliate against a cyber attack is a complicated decision, and a new framework guided by game theory could help policymakers determine the best strategy.The "Blame Game" was d...
Novel technique tracks more web users across browsers
Novel technique tracks more web users across browsers
2017/3/13
For good or ill, what users do on the web is tracked. Banks track users as an authentication technique, to offer their customers enhanced security protection. Retailers track customers and potential c...
Reliability measures of electrical grid has risen to a new norm as it involves physical security and cybersecurity. Threats to either can trigger instability, leading to blackouts and economic losses....
Your 'anonymized' web browsing history may not be anonymous
anonymized web browsing history may not be anonymous
2017/2/16
Raising further questions about privacy on the internet, researchers from Princeton and Stanford universities have released a study showing that a specific person's online behavior can be identified b...
Cyberattacks on corporations, agencies, national infrastructure and individuals have exposed the fragility and vulnerability of the internet and networked systems. Achieving truly secure cyberspace re...
This century, our world will be flooded with hundreds of billions of smartphones, gadgets, sensors and other smart objects connected to the internet.They will perform myriad services, such as mon...
Setting up a decoy network may help deflect a hacker's hits
decoy network deflect a hacker hits
2016/9/29
Computer networks may never float like a butterfly, but Penn State information scientists suggest that creating nimble networks that can sense jabs from hackers could help deflect the stinging blows o...
NSF awards $110 million to bring advanced cyberinfrastructure to nation’s scientists,engineers
NSF awards $110 million advanced cyberinfrastructure nation’s scientists engineers
2016/9/12
Today, the National Science Foundation (NSF) announced a $110 million award to the University of Illinois at Urbana-Champaign and 18 partner institutions to continue and expand activities undertaken t...
As the world grows more social and connects more online, privacy management is becoming more collaborative, according to Penn State researchers."This is a paradigm shift, in a lot of ways, because mos...
Statement from France Cordova in support of Federal Cybersecurity Research and Development Strategic Plan
France Cordova Federal Cybersecurity Research and Development Strategic Plan
2016/2/23
"Investments in fundamental research by the National Science Foundation (NSF) have resulted in innovative ways to secure information and enhance privacy in an increasingly connected society," said Fra...
Roadmap to safer cyberspace
Roadmap safer cyberspace
2015/12/22
How do cybersecurity experts discover how to properly defend a system or build a network that's secure?As in other domains of science, this process involves hypothesis, experimentation, and analysis -...
“无线调频”技术可提升网速
无线调频 网速
2015/11/11
美国西北大学2015年11月9日发布新闻公报称,该校研究人员研发出一种“无线调频”技术。该技术可根据调频信号判断收发数据的最佳时间,疏解网络拥堵,进而提升网速。

